Custom Framework
.png)
Custom Framework
.png)
Anecdotes’ data-first mindset and unique approach to cross-mapping enable continuous monitoring of any custom framework. No need to rely on error-prone manual work. Based on your list of controls, our in-house developed AI will automatically map requirements to your controls, ensuring your custom framework is fully integrated with the rest of your GRC program. That means you can continue enjoying automated evidence collection and eliminate the need for duplicate work.
Stage 1
Create your list of controls.
Reasons you might need a custom framework include:
Frameworks that are based on your audit requirements or that rely on custom controls that best fit your business.
Frequently used by enterprises to prioritize and standardize key GRC requirements and by internal audit teams to form a common language with the GRC team.
Frameworks consisting of controls that customers ask to inspect as a part of their security review process.
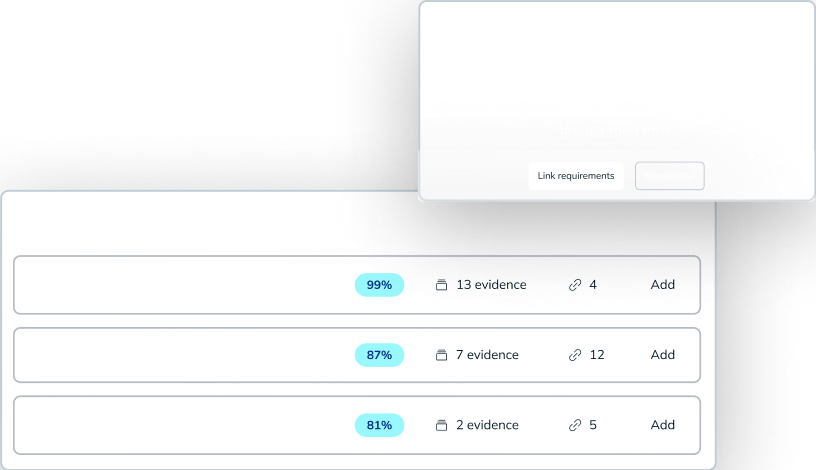
Stage 2
Without Anecdotes: For each control, you need to define what requirements have to be met in order to satisfy it. This mapping, especially if you have a large tech stack, can be a huge undertaking, and it never really ends since your organization is continually adopting new tools.
Based on your list of controls, Anecdotes’ AI automatically maps requirements to your controls. You can choose to accept all of the recommendations in bulk or to go through them one-by-one. Our AI can always suggest additional requirements in the future and you can, of course, add requirements manually.
Stage 3
Without Anecdotes: Once you know what needs to be monitored, it's time to start monitoring. You need to manually collect evidence from your tools and control owners, over and over again, and then validate it.
Because your controls are now automatically populated by Anecdotes’ cross-mapped requirements, you will continue to enjoy automated evidence collection, allowing you to continuously monitor your custom framework the same way you would out-of-the-box frameworks.
%20(1).png)